Cybersecurity Monthly Report (December 2025)
Cybersecurity Monthly Report (December2025)
1. Recent Policy Highlights
The amendment to the Cyber Security Management Act officially came into effect on December 1, 2025. Pursuant to the authorization under Article 11, Paragraph 3 of the Act, the Ministry promulgated the Regulations on the Review of Products Endangering National Cyber Security on December 19, 2025 (Order No. 1145000392), with retroactive effect from December 1, 2025. In addition, reporting forms for intelligence on products harmful to national cybersecurity have been announced and made available in the “Cybersecurity Laws and Regulations” section of the Administration for Cyber Security official website
(https://moda.gov.tw/ACS/laws/regulations/18146).
On December 23, 2025, the Legislative Yuan passed the Artificial Intelligence Fundamental Act on its third reading. The Act aims to promote human-centered artificial intelligence research and development and foster the growth of the AI industry, establish a secure AI application environment, advance digital inclusion, and safeguard fundamental rights. It is intended to ensure that technological applications align with social ethics, preserve national cultural values, enhance international competitiveness, and establish a sound legal framework.
2. Recent Cybersecurity Incident Sharing
Exploitation of an SSL VPN Vulnerability to Implant Database Malware
Abnormal connections were detected on an agency’s website. Subsequent investigation revealed that attackers exploited a vulnerability in the SSL VPN functionality to successfully log in and create new accounts, followed by lateral movement to a database server where malware was implanted. During the incident, multiple cybersecurity risks were identified, including outdated firewall firmware, expired intrusion prevention system licenses, and unrestricted access to administrative interfaces. The agency disconnected the affected equipment from the network and conducted forensic analysis and incident response actions.
Lessons Learned
The root causes of this incident were primarily attributed to four factors: expired security licenses, deficiencies in firmware and vulnerability maintenance, weaknesses in account privilege management, and overly permissive external access controls. Due to the failure to update security device firmware in a timely manner, attackers were able to exploit known vulnerabilities in combination with proof-of-concept (PoC) tools to bypass authentication mechanisms and gain system access, subsequently implanting malware through the unauthorized creation of accounts. To prevent similar incidents from recurring, the following protective measures are provided for reference:
Ensure Continuous Effectiveness of Cybersecurity Protection
Establish license expiration alert mechanisms to ensure that security devices (such as IPS and web filtering systems) maintain valid licenses, enabling automatic signature updates to address emerging threats.
Firmware Updates and Vulnerability Mitigation
Incorporate security device firmware into regular update schedules and verify the remediation status of known vulnerabilities.
Account Management Controls
Review system accounts for any abnormal additions, and disable or remove unused services and accounts.
Enforcement of Remote Access Restrictions
Remote access services (such as SSL VPN and SSH) should be implemented in accordance with the principles of “prohibition by default with exceptions allowed” and the “principle of least privilege,” as outlined in Executive Yuan official guidance (Order No. 1100165761).
3. Cybersecurity Trends
3.1 National Government Cybersecurity Threat Trends
Ex ante joint defense and monitoring
This month, a total of 61,580 cybersecurity joint defense intelligence items were collected from government agencies (a decrease of 1,215 items). Among identifiable threat categories, information collection ranked first (45%), primarily involving scanning, probing, and social engineering techniques. This was followed by intrusion attempts (21%), mainly involving attempts to intrude into unauthorized hosts, and intrusion attacks (18%), most of which involved unauthorized system access or the acquisition of system or user privileges. Statistics on the distribution of intelligence over the past year are shown in Figure 1.
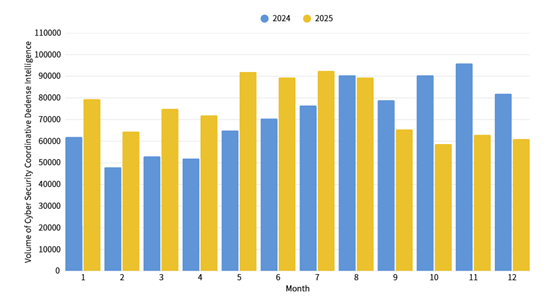
Figure 1: Statistics of cybersecurity monitoring intelligence in joint defense
Hackers Hide Malware in Legitimate Websites to Evade Detection
After further compilation and analysis of joint defense intelligence information, it was recently discovered that attackers have abused Microsoft Cabinet (CAB) files as malware delivery vehicles in social engineering phishing emails. CAB files are a commonly used compression and packaging format in Microsoft environments and are widely applied in Windows updates, driver deployment, and installation processes. Due to their flexibility and legitimacy, CAB files are frequently abused by attackers to conceal malicious content or reduce file signature visibility. Attackers embed malicious executables within CAB files to bypass security detection mechanisms and lure recipients into executing malicious content. Relevant intelligence and defensive recommendations have been provided to government agencies for joint monitoring and protection.
In-Process Reporting and Responding
The number of cybersecurity incident reports totaled 107 this month, representing 1.67 times the number reported during the same period last year. The primary type of reported incidents was illegal intrusion, accounting for 71.57% of all cases. This month, multiple agencies were again found to have been compromised through the installation of counterfeit software, resulting in malware infections, which accounted for 32.71% of reported incidents. Statistics for cybersecurity incident reports over the past year are shown in Figure 2.
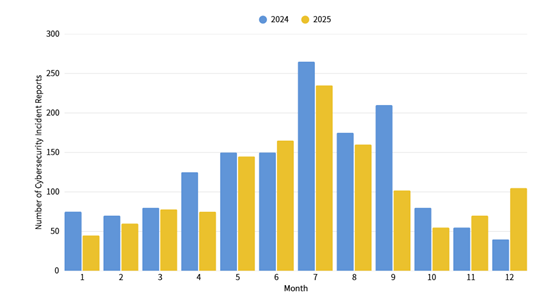
Figure 2: Statistics of cybersecurity incident reports
3.2 Important Vulnerability Alerts
| Alert Type | Category | Description |
|---|---|---|
| Vulnerability Alert |
Compression Software: 7-Zip (versions earlier than 25.01) |
|
| WordPress Plugins and Themes Contain Ten High-Risk Security Vulnerabilities Severity: CVSS 9.8 (CVE-2025-67522 CVE-2025-67523 CVE-2025-67524 CVE-2025-67525 CVE-2025-67526 CVE-2025-67527 CVE-2025-67529 CVE-2025-67530 CVE-2025-67531 CVE-2025-67532) |
|
|
| Remote Device Management Software: Advantech WISE-DeviceOn Server Severity: CVSS 9.8 (CVE-2025-34256) |
|
|
| Known Exploited Vulnerability |
Operating System: Cisco AsyncOS |
|
|
Open-source JavaScript Library: React Server Components |
|
Alert Explanations:
Vulnerability Alert: Verified vulnerabilities that have not yet been widely exploited by attackers. It is recommended to arrange updates as soon as possible.
Known Exploited Vulnerability: Known instances of successful attacks exploiting the vulnerability. Immediate evaluation and patching are strongly recommended.
4. International Cybersecurity News
CISA and NSA Issue Warning on China-linked “BRICKSTORM” Malware (Source: The Record)
On December 4, the U.S. Cybersecurity and Infrastructure Security Agency (CISA), the National Security Agency (NSA), and the Canadian Centre for Cyber Security (CCS) jointly issued an alert regarding the BRICKSTORM malware, based on samples obtained from victim organizations. BRICKSTORM is a sophisticated backdoor malware associated with a China state-sponsored threat actor. It primarily targets government and IT sector organizations and is capable of maintaining long-term persistence within compromised systems. The malware mainly affects VMware vSphere and Windows environments and can be used to extract credentials and create hidden virtual machines for covert access. It also features self-monitoring capabilities, enabling automatic reinstallation or restart if disrupted. In addition, it has been observed being used for file browsing, uploading, downloading, creation, deletion, and modification, as well as lateral movement to compromise additional systems. CISA officials declined to confirm whether U.S. federal agencies were affected.
NIST Plans to Develop an AI Agent Threat and Mitigation Taxonomy (Source: Security Boulevard)
The U.S. National Institute of Standards and Technology (NIST) is developing a taxonomy for AI agent threats and mitigation measures to address the growing security risks associated with the rapid adoption of artificial intelligence. The initiative was announced at an AI summit in New York and aims to systematically identify and classify attack surfaces unique to AI agents, thereby strengthening existing cybersecurity frameworks that are currently insufficient for protecting enterprise AI applications. NIST emphasized the urgency of this effort, citing cases in which security researchers successfully extracted sensitive data from large language models (LLMs). As organizations increasingly experiment with more autonomous AI agents, this taxonomy will provide critical guidance for managing emerging digital identities and permissions, as well as mitigating risks such as shadow AI and real-time prompt injection attacks.
5. Cybersecurity Awareness Information
5.1 Government Configuration Baseline (GCB) Development Updates
The Government Configuration Baseline (GCB) aims to standardize secure configuration settings for information and communications equipment such as personal computers, servers, and network devices (e.g., password length and update cycles) in order to reduce the risk of being exploited as intrusion vectors and subsequently triggering cybersecurity incidents.
The 2025 GCB development initiatives include Apple macOS 15, Safari, AWS infrastructure, and Fortinet FortiGate. In addition, draft documentation for the 2026 GCB and the “2026 Government Configuration Baseline (GCB) Feedback Form v1.0” have been published in the GCB section (https://s.moda.gov.tw/2mtunS9EnATA). Agencies are welcome to download the materials and submit completed feedback forms via email by June 30, 2026, to provide suggestions for adjustments and revisions. For inquiries, agencies may contact the Assessment and Defense Center of the National Institute of Cyber Security at (02) 2739-1000 ext. 23.
5.2 Call for Agencies at Cybersecurity Responsibility Level C or Above to Actively Submit Positions for the Civil Service Senior Examination (Cybersecurity Category)
To address cybersecurity workforce demands across government agencies, a Cybersecurity Category was added to the Civil Service Level 3 Senior Examination starting in 2024 to recruit newly appointed civil servants with cybersecurity expertise and establish a stable, long-term cybersecurity talent pipeline for the government. Agencies are requested to submit relevant position openings in accordance with the schedule announced by the Directorate-General of Personnel Administration, Executive Yuan, in order to recruit cybersecurity professionals and strengthen organizational cybersecurity protection capabilities.
6. Recent Key Cybersecurity Meetings and Activities
| Date | Event/Meeting | Audience |
|---|---|---|
|
January 9 |
Cybersecurity Skills Golden Shield Award Finals and Award Ceremony |
Secondary school and university students participating in the Cybersecurity Skills Golden Shield Award |
| January 16–17 | Cybersecurity Elite Course: Elite Alumni Day | Graduates of the Cybersecurity Elite Course from previous cohorts (2021–2024) |